NIS2 in Practice: An Operational Checklist to Comply Without Slowing Down the Business
Over the past few months, we’ve talked extensively about NIS2: what it requires, which sectors are affected, and why it represents a major shift in the way security is managed. The picture is now clear: the directive is no longer a topic reserved for specialists—it is a concrete requirement that impacts processes, suppliers, and management responsibilities
13 Apr

Cyber Security in the PA: risks, planned interventions, solutions
Cyber security concerns everyone and involves both private subjects and public bodies. Within public administration, the issue of cyber security is now of an urgent nature: in recent years, in fact, the vulnerability of the PA’s IT system, which stores and collects sensitive data, has caused considerable damage. The digital evolution of the bodies capable of guaranteeing the...
06 Jun

Remote Working: how your employees can work from home while keeping data safe
Remote working is becoming increasingly important for companies. The spread of the Coronavirus pandemic in 2020 accelerated the phenomenon – which was already underway – and over the last two years, companies have been able to see that what appeared to be the consequence of an emergency (remote working) can actually be considered an opportunity to be exploited, to...
14 Mar
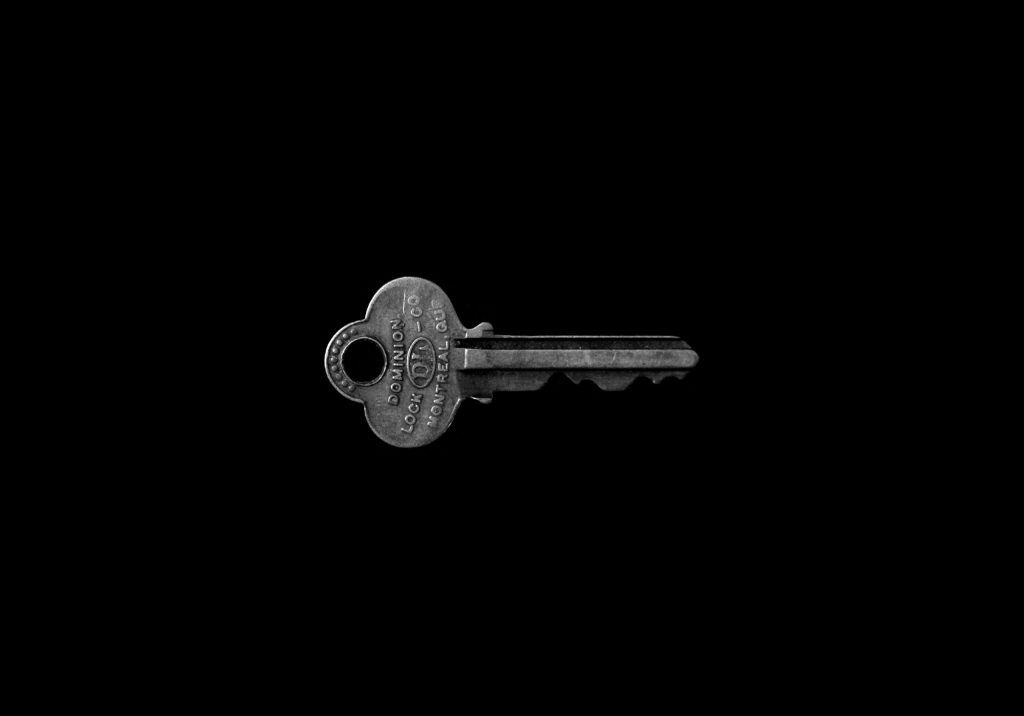
Encryption and ransomware: how to prevent attacks and increase cybersecurity in business
The central topics of this article are encryption and ransomware: we will analyze, in particular, the relationship between the two and the fundamental role that the use of cryptographic keys plays in protecting the business of companies.Businesses today cannot avoid obtaining high-level protection from the damage caused by various types of cyber attacks and their...
14 Jan



